|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA316] DSA-316-1 nethack Vulnerability Assessment Details
|
[DSA316] DSA-316-1 nethack |
||
|
DSA-316-1 nethack Detailed Explanation for this Vulnerability Assessment The nethack and slashem packages are vulnerable to a buffer overflow exploited via a long '-s' command line option. This vulnerability could be used by an attacker to gain gid 'games' on a system where nethack is installed. Additionally, some setgid binaries in the nethack package have incorrect permissions, which could permit a user who gains gid 'games' to replace these binaries, potentially causing other users to execute malicious code when they run nethack. Note that slashem does not contain the file permission problem CVE-2003-0359. For the stable distribution (woody) these problems have been fixed in version 3.4.0-3.0woody3. For the old stable distribution (potato) these problems have been fixed in version 3.3.0-7potato1. For the unstable distribution (sid) these problems are fixed in version 3.4.1-1. We recommend that you update your nethack package. For the stable distribution (woody) these problems have been fixed in version 0.0.6E4F8-4.0woody3. For the old stable distribution (potato) these problems have been fixed in version 0.0.5E7-3potato1. For the unstable distribution (sid) these problems are fixed in version 0.0.6E4F8-6. We recommend that you update your slashem package. Solution : http://www.debian.org/security/2003/dsa-316 Network Security Threat Level: High Networks Security ID: 6806, 7953 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Apple Macintosh Performa 466 Vintage Computer | SKU 146754
$149.95
Vintage Apple IIe (2e) Computer, monitor, joystick, cooling fan, floppy set
$329.00
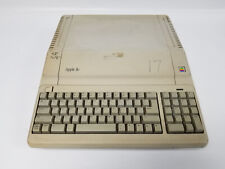
Vintage Apple IIe Computer A2S2128 (Powers On)
$189.99
Vintage Apple M2980 AppleDesign Keyboard - Tested and working - Good condition
$19.75
Vintage Apple III Brochure for BPI Accounting Series, very nice condition
$50.00
Vintage Apple Computer Monitor
$45.90
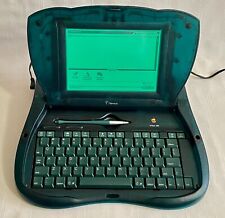
Vintage Apple Newton eMate 300 Laptop Computer 1997 H0208 Teal Blue Green Last 1
$194.99
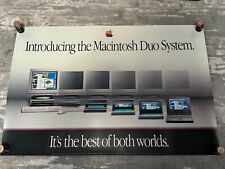
Vintage Apple "Introducing the Macintosh Duo System" Poster
$100.00
Vintage Apple Keyboard & Mouse Translucent Blue M2452/M4848 Good Condition
$49.95
Vintage Apple M7803 Pro USB Wired Keyboard Clear Black 2000
$24.99
|
||
|
No Discussions have been posted on this vulnerability. |