|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA272] DSA-272-1 dietlibc Vulnerability Assessment Details
|
[DSA272] DSA-272-1 dietlibc |
||
|
DSA-272-1 dietlibc Detailed Explanation for this Vulnerability Assessment eEye Digital Security discovered an integer overflow in the xdrmem_getbytes() function of glibc, that is also present in dietlibc, a small libc useful especially for small and embedded systems. This function is part of the XDR encoder/decoder derived from Sun's RPC implementation. Depending upon the application, this vulnerability can cause buffer overflows and could possibly be exploited to execute arbitrary code. For the stable distribution (woody) this problem has been fixed in version 0.12-2.5. The old stable distribution (potato) does not contain dietlibc packages. For the unstable distribution (sid) this problem has been fixed in version 0.22-2. We recommend that you upgrade your dietlibc packages. Solution : http://www.debian.org/security/2003/dsa-272 Network Security Threat Level: High Networks Security ID: 7123 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

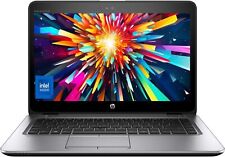
~DAILY DEALZ~ 14" HP EliteBook Laptop PC: Intel i5 16GB RAM 256GB SSD Webcam
$229.99
Team T-FORCE VULCAN Z 16GB (2 x 8GB) 288-Pin PC RAM DDR4 3200 (PC4 25600) XMP
$38.99
A-Tech 8GB DDR3 1600 PC3-12800 Laptop SODIMM 204-Pin Memory RAM PC3L DDR3L 1x 8G
$13.99
HyperX FURY RAM DDR4 16GB 8GB 32GB 4GB 3200 2666 2400 2133 Desktop Memory DIMM
$14.85
HyperX FURY DDR3 8GB 16GB 32GB 1600 MHz PC3-12800 Desktop RAM Memory DIMM 240pin
$12.90
Crucial 16GB (2x 8GB) Kit DDR3L 1600MHz PC3-12800 UDIMM Desktop 240-Pin CL11 RAM
$21.33
CORSAIR Vengeance RGB Pro 32GB (2 x 16GB) 288-Pin PC RAM DDR4 3600 (PC4 28800)
$79.95
Crucial DDR3L 16GB 1600 2x 8GB PC3-12800 Laptop SODIMM Memory RAM PC3 16G DDR3
$21.50
Lenovo ThinkBook 14-IIL i7-1065G7 4GB RAM 256GB SSD DAMAGED BAD TRACKPAD Read
$89.99
HyperX FURY DDR4 16GB 32GB 64GB 2666MHz PC4-21300 Desktop RAM Memory DIMM 288Pin
$119.80
|
||
|
No Discussions have been posted on this vulnerability. |