|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA218] DSA-218-1 bugzilla Vulnerability Assessment Details
|
[DSA218] DSA-218-1 bugzilla |
||
|
DSA-218-1 bugzilla Detailed Explanation for this Vulnerability Assessment A cross site scripting vulnerability has been reported for Bugzilla, a web-based bug tracking system. Bugzilla does not properly sanitize any input submitted by users for use in quips. As a result, it is possible for a remote attacker to create a malicious link containing script code which will be executed in the browser of a legitimate user, in the context of the website running Bugzilla. This issue may be exploited to steal cookie-based authentication credentials from legitimate users of the website running the vulnerable software. This vulnerability only affects users who have the 'quips' feature enabled and who upgraded from version 2.10 which did not exist inside of Debian. The Debian package history of Bugzilla starts with 1.13 and jumped to 2.13. However, users could have installed version 2.10 prior to the Debian package. For the current stable distribution (woody) this problem has been fixed in version 2.14.2-0woody3. The old stable distribution (potato) does not contain a Bugzilla package. For the unstable distribution (sid) this problem will be fixed soon. We recommend that you upgrade your bugzilla packages. Solution : http://www.debian.org/security/2002/dsa-218 Network Security Threat Level: High Networks Security ID: 6257 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Cisco SG95-16 16-Port Gigabit Switch SG95-16-KR
$47.00
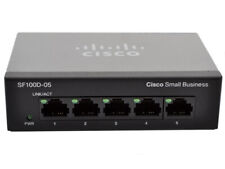
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
8 Ports Unmanaged Industrial Ethernet Switch Network Gigabit Ethernet Switch
$76.50
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
HP 2530-48G 48 Port Gigabit Ethernet Network Switch J9775A
$30.95
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
HP ProCurve 2530-24G J9776A 24 Port Gigabit Ethernet Managed Network Switch
$34.99
Netgear Prosafe Plus JGS524PE 24 Port Gigabit Switch 12 Port PoE JGS524PE-100NAS
$129.98
HP JG937A Flexnetwork 5130-48G PoE+ 48-Port Gigabit Network Switch
$65.95
|
||
|
No Discussions have been posted on this vulnerability. |