|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA204] DSA-204-1 kdelibs Vulnerability Assessment Details
|
[DSA204] DSA-204-1 kdelibs |
||
|
DSA-204-1 kdelibs Detailed Explanation for this Vulnerability Assessment The KDE team has discovered a vulnerability in the support for various network protocols via the KIO. The implementation of the rlogin and telnet protocols permits a carefully crafted URL in an HTML page, HTML email or other KIO-enabled application to execute arbitrary commands on the system using the victim's account on the vulnerable machine. This problem has been fixed by disabling rlogin and telnet in version 2.2.2-13.woody.5 for the current stable distribution (woody). The old stable distribution (potato) is not affected since it doesn't contain KDE. A correction for the package in the unstable distribution (sid) is not yet available. We recommend that you upgrade your kdelibs3 package immediately. Solution : http://www.debian.org/security/2002/dsa-204 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Extron RGB-160XI Analog Computer Video 60-378-01
$187.06
The analog thing modern open source, educational, low-cost analog computer
$800.00
Vintage 1960s Donner Model 3000 Analog Computer ~ MUSEUM PIECE Extremely Rare
$4000.00
NEW Aquarius+ Computer Signature Edition - 8Bit Retro System
$229.00
Apple Macintosh SE/30 M5119 Computer 8MB RAM Recapped Working *See Description*
$475.00
Apple IIc Analog Board NOS - 661-0265
$74.00
IBM Modem Saver Phone Line Tester
$7.99
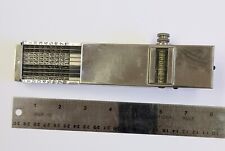
Landen Computer. Circa 1898. the Rapid Computer Company. With Original Case.
$425.00
ACASIS PCIE Capture Card HDMI 1.4 1080P60HZ PCIE 2.0 X4 20Gbps for Video Capture
$248.99
MultiTech FaxFinder FF240 Windows Fax Server SKU92500751LF Analog 1N22860#3
$139.49
|
||
|
No Discussions have been posted on this vulnerability. |