|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA188] DSA-188-1 apache-ssl Vulnerability Assessment Details
|
[DSA188] DSA-188-1 apache-ssl |
||
|
DSA-188-1 apache-ssl Detailed Explanation for this Vulnerability Assessment According to David Wagner, iDEFENSE and the Apache HTTP Server Project, several vulnerabilities have been found in the Apache package, a commonly used webserver. Most of the code is shared between the Apache and Apache-SSL packages, so vulnerabilities are shared as well. These vulnerabilities could permit a possible hacker to enact a denial of service against a server or execute a cross scripting attack, or steal cookies from other web site users. Vulnerabilities in the included legacy programs htdigest, htpasswd and ApacheBench can be exploited when called via CGI. Additionally the insecure temporary file creation in htdigest and htpasswd can also be exploited locally. The Common Vulnerabilities and Exposures (CVE) project identified the following vulnerabilities: This is the same vulnerability as CVE-2002-1233, which was fixed in potato already but got lost later and was never applied upstream. (binaries not included in apache-ssl package though) These problems have been fixed in version 1.3.26.1+1.48-0woody3 for the current stable distribution (woody) and in 1.3.9.13-4.2 for the old stable distribution (potato). Corrected packages for the unstable distribution (sid) are expected soon. We recommend that you upgrade your Apache-SSL package immediately. Solution : http://www.debian.org/security/2002/dsa-188 Network Security Threat Level: High Networks Security ID: 5847, 5884, 5887, 5995 Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
A8PicoCart Kit Atari XE XL unocart clone multicart cartridge game
$18.95
Atari 600 XL Vintage Home Computer - New in Box, Unused
$200.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
ATARI XEGS Game System Tested Working CIB Complete in LATE CHILEAN RETAIL box
$590.00
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
Vintage Atari 800XL Computer With Original Box
$140.00
Atari 520 1040 ST Astra Systems 4 Meg Computer Memory Card 4MB
$49.00
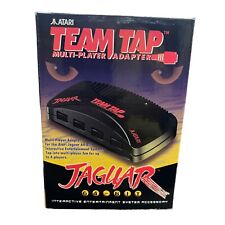
TEAM TAP Atari Jaguar Multi Player Adapter NEW In Box
$25.46
Atari 65xe nice condition (800xl compatible)
$225.00
|
||
|
No Discussions have been posted on this vulnerability. |