|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA148] DSA-148-1 hylafax Vulnerability Assessment Details
|
[DSA148] DSA-148-1 hylafax |
||
|
DSA-148-1 hylafax Detailed Explanation for this Vulnerability Assessment A set of problems have been discovered in Hylafax, a flexible client/server fax software distributed with many GNU/Linux distributions. Quoting SecurityFocus the problems are in detail: These problems have been fixed in version 4.0.2-14.3 for the old stable distribution (potato), in version 4.1.1-1.1 for the current stable distribution (woody) and in version 4.1.2-2.1 for the unstable distribution (sid). We recommend that you upgrade your hylafax packages. Solution : http://www.debian.org/security/2002/dsa-148 Network Security Threat Level: High Networks Security ID: 3357, 5348, 5349 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Vintage IBM KB-7993 white PS/2 keyboard plus 7 extra buttons, 6 vol. controls
$22.95
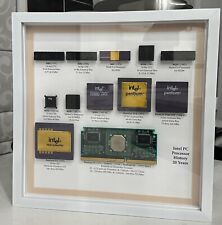
Vintage Intel Personal PC CPU Collection in White Shadowbox Display
$200.00
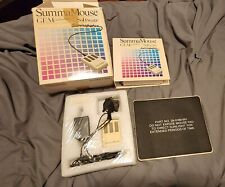
VINTAGE SummaGraphics SummaMouse
$240.00
Vintage Sensomotoric Instruments Computer Keyboard
$30.00
Vintage COMPAQ 122873-001, 12/24GB DDS DAT tape drive FOR PARTS OR REPAIR
$100.00
Vintage Classic Apple Macintosh System Boot Install Disk Floppy/CD *Pick Version
$10.39
Z80 - NABU PC & Keyboard - Vintage New Old Stock (Retro 80's)
$139.99
Drakware ADB2USB - vintage Apple ADB to USB keyboard adapter
$29.95
SEALED Vintage Western Digital Value Line Hard Drive 3.5-Inch Enhanced IDE 25 GB
$100.00
Vintage Compaq Presario Mouse, Model MUS9J, PS/2 - Tested & Working, Very Good
$12.99
|
||
|
No Discussions have been posted on this vulnerability. |