|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA142] DSA-142-1 openafs Vulnerability Assessment Details
|
[DSA142] DSA-142-1 openafs |
||
|
DSA-142-1 openafs Detailed Explanation for this Vulnerability Assessment An integer overflow bug has been discovered in the RPC library used by the OpenAFS database server, which is derived from the SunRPC library. This bug could be exploited to crash certain OpenAFS servers (volserver, vlserver, ptserver, buserver) or to obtain unauthorized root access to a host running one of these processes. No exploits are known to exist yet. This problem has been fixed in version 1.2.3final2-6 for the current stable distribution (woody) and in version 1.2.6-1 for the unstable distribution (sid). Debian 2.2 (potato) is not affected since it doesn't contain OpenAFS packages. OpenAFS is only available for the architectures alpha, i386, powerpc, s390, sparc. Hence, we only provide fixed packages for these architectures. We recommend that you upgrade your openafs packages. Solution : http://www.debian.org/security/2002/dsa-142 Network Security Threat Level: High Networks Security ID: 5356 Vulnerability Assessment Copyright: This script is (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
Samsung Galaxy 12.4 Inch EF-DT730 Slim Keyboard For S7+ | S7 FE | S8+ | S8+ 5G
$39.99
Samsung - S Pen Creator Edition - White
$40.00
Samsung Galaxy Chromebook Go, 14-inch, 32GB, Unlocked All Carriers - Silver
$99.95
Samsung 27" FHD Monitor 75 hz, IPS LED, LF27T350FHNXZA *READ DISCRIPTION*
$74.99
Samsung 16GB 2Rx4 PC3-12800R M393B2G70BH0-CK0 DDR3 RDIMM - SERVER RAM
$8.90
Samsung Laptop Chromebook XE303C12-A01US, Dual-Core 1.7GHz 4GB 16GB
$39.99
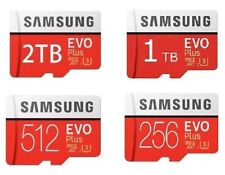
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
|
||
|
No Discussions have been posted on this vulnerability. |