|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA136] DSA-136-1 openssl Vulnerability Assessment Details
|
[DSA136] DSA-136-1 openssl |
||
|
DSA-136-1 openssl Detailed Explanation for this Vulnerability Assessment The OpenSSL development team has announced that a security audit by A.L. Digital Ltd and The Bunker, under the DARPA CHATS program, has revealed remotely exploitable buffer overflow conditions in the OpenSSL code. Additionally, the ASN1 parser in OpenSSL has a potential DoS attack independently discovered by Adi Stav and James Yonan. CVE-2002-0655 references overflows in buffers used to hold ASCII representations of integers on 64 bit platforms. CVE-2002-0656 references buffer overflows in the SSL2 server implementation (by sending an invalid key to the server) and the SSL3 client implementation (by sending a large session id to the client). The SSL2 issue was also noticed by Neohapsis, who have privately demonstrated exploit code for this issue. CVE-2002-0659 references the ASN1 parser DoS issue. These vulnerabilities have been addressed for Debian 3.0 (woody) in openssl094_0.9.4-6.woody.2, openssl095_0.9.5a-6.woody.1 and openssl_0.9.6c-2.woody.1. These vulnerabilities are also present in Debian 2.2 (potato). Fixed packages are available in openssl094_0.9.4-6.potato.2 and openssl_0.9.6c-0.potato.4. A worm is actively exploiting this issue on internet-attached hosts we recommend you upgrade your OpenSSL as soon as possible. Note that you must restart any daemons using SSL. (E.g., ssh or ssl-enabled apache.) If you are uncertain which programs are using SSL you may choose to reboot to ensure that all running daemons are using the new libraries. Solution : http://www.debian.org/security/2002/dsa-136 Network Security Threat Level: High Networks Security ID: 5353, 5361, 5362, 5363, 5364, 5366 Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
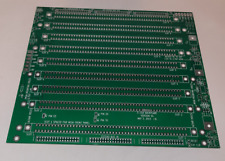
S-100 backplane motherboard bare PCB 9 slot (for Altair/IMSAI)
$30.00
Altair MITS 8800 CPU Parts Kit not IMSAI 8080 S100 (board NOT included)
$64.95
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
$22.50
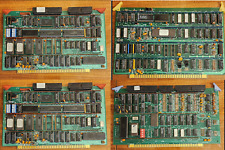
Vintage Rare S100 Card Bundle - Includes CPU / processor / Interface / Port Card
$395.00
VINTAGE DEC 1975 VOL 1 ISSUE 1 SCCS INTERFACE MAGAZINE MITS ALTAIR COVER & ADS
$359.99
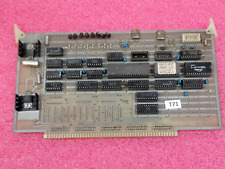
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
|
||
|
No Discussions have been posted on this vulnerability. |