|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1188] DSA-1188-1 mailman Vulnerability Assessment Details
|
[DSA1188] DSA-1188-1 mailman |
||
|
DSA-1188-1 mailman Detailed Explanation for this Vulnerability Assessment Several security related problems have been discovered in mailman, the web-based GNU mailing list manager. The Common Vulnerabilities and Exposures project identifies the following problems: Moritz Naumann discovered several cross-site scripting problems that could permit remote attackers to inject arbitrary web script code or HTML. Moritz Naumann discovered that a remote attacker can inject arbitrary strings into the logfile. For the stable distribution (sarge) these problems have been fixed in version 2.1.5-8sarge5. For the unstable distribution (sid) these problems have been fixed in version 2.1.8-3. We recommend that you upgrade your mailman package. Solution : http://www.debian.org/security/2006/dsa-1188 Network Security Threat Level: High Networks Security ID: 19831 Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

***NEW*** BCM RX67Q Gaming Motherboard | Intel Q67 2nd/3rd Gen. | LGA1155 | DDR3
$29.77
ASUS H110M-R Motherboard Intel 6th/7th Gen LGA1151 DDR4 Micro-ATX i/o shield
$42.00
GIGABYTE B560M DS3H AC LGA1200 Intel B560 SATA 6Gb/s Micro ATX Intel Motherboard
$64.99
Micro ATX Desktop Motherboard ASUS H110M-C LGA 1151
$31.95
MSI B450M PRO-VDH MAX AM4 AMD B450 USB3.2 Micro-ATX Motherboard
$67.99
Gigabyte AMD B550 UD AC Gaming Motherboard - AMD B550 Chipset - AM4 Socket - AMD
$89.99
Asrock Z390 Phantom Gaming 4S/AC Wifi 8th/9th Gen Intel 1151 Motherboard Bulk
$48.70
ASUS H110M-C Micro-ATX DDR4 LGA1151 & I3-6100
$35.00
GIGABYTE MB10-Datto Motherboard Xeon D-1521- SR2DF 2.40 GHz- Open Box
$112.00
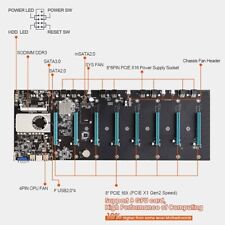
BTC-S37 Mining Motherboard Kit /w SSD & Ram Preinstalled
$59.99
|
||
|
No Discussions have been posted on this vulnerability. |