|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1176] DSA-1176-1 zope2.7 Vulnerability Assessment Details
|
[DSA1176] DSA-1176-1 zope2.7 |
||
|
DSA-1176-1 zope2.7 Detailed Explanation for this Vulnerability Assessment It was discovered that the Zope web application server does not disable the csv_table directive in web pages containing ReST markup, permiting the exposure of files readable by the Zope server. For the stable distribution (sarge) this problem has been fixed in version 2.7.5-2sarge2. The unstable distribution (sid) doesn't contain zope2.7 any longer, for zope2.8 this problem has been fixed in version 2.8.8-2. We recommend that you upgrade your Zope package. Solution : http://www.debian.org/security/2006/dsa-1176 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Cisco SG95-16 16-Port Gigabit Switch SG95-16-KR
$47.00
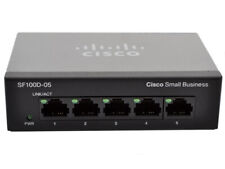
Cisco (SG100D-05-UK) 5-Ports External Ethernet Switch
$40.00
Cisco SG110 24 Port Gigabit Ethernet Switch w/ 2 x SFP SG110-24
$117.00
HP 2530-48G 48 Port Gigabit Ethernet Network Switch J9775A
$30.95
New Linksys SE3005 5-port Gigabit Ethernet Switch
$18.99
Linksys SE3008 8 Ports Rack Mountable Gigabit Ethernet Switch
$21.99
HP ProCurve 2530-24G J9776A 24 Port Gigabit Ethernet Managed Network Switch
$34.99
NetGear ProSafe GS748T V4 48-Port Gigabit Smart Switch w/ Ears + Cord
$35.00
Netgear Prosafe Plus JGS524PE 24 Port Gigabit Switch 12 Port PoE JGS524PE-100NAS
$129.98
Juniper Networks EX3300-48P 48-Port PoE+ 4x SFP+ Network Switch w/ Power Cord
$43.95
|
||
|
No Discussions have been posted on this vulnerability. |