|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1149] DSA-1149-1 ncompress Vulnerability Assessment Details
|
[DSA1149] DSA-1149-1 ncompress |
||
|
DSA-1149-1 ncompress Detailed Explanation for this Vulnerability Assessment Tavis Ormandy from the Google Security Team discovered a missing boundary check in ncompress, the original Lempel-Ziv compress and uncompress programs, which permits a specially crafted datastream to underflow a buffer with attacker controlled data. For the stable distribution (sarge) this problem has been fixed in version 4.2.4-15sarge2. For the unstable distribution (sid) this problem has been fixed in version 4.2.4-15sarge2. We recommend that you upgrade your ncompress package. Solution : http://www.debian.org/security/2006/dsa-1149 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

NetFu Firewall 1U, Intel CPU, 8 x Gigabit, SFP, w/ pfSense, Others, NEW OPTIONS
$509.58
NEW NetFu Firewall Mini, Intel CPU, 6 Port Gigabit, w/ pfSense, others
$325.60
Cisco ASA5525-FTD-K9 Security Appliance with FirePower Services
$1000.00
Fortinet Fortigate FG-61E | Firewall Network Security Appliance
$49.99
Fortinet FortiGate FG-40F Network Security Firewall
$100.00
OPNsense six-port Gigabit router/firewall on Lanner FW-7535 hardware
$69.00
Fortinet Fortiwifi 60D FWF-60D Security Appliance Firewall Wifi VPN
$29.99
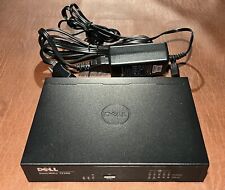
Dell SonicWall TZ300 5-Port Network Security Firewall Appliance APL28-0B4
$24.95
Fortinet Fortiwifi 60D FG-60D Security Appliance Firewall / VPN w/ AC Adapter
$999.97
FORTINET FG-500D FortiGate 500D, 10xGE RJ45 ports, 8xGE SFP slots Firewall
$126.00
|
||
|
No Discussions have been posted on this vulnerability. |