|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1137] DSA-1137-1 tiff Vulnerability Assessment Details
|
[DSA1137] DSA-1137-1 tiff |
||
|
DSA-1137-1 tiff Detailed Explanation for this Vulnerability Assessment Tavis Ormandy of the Google Security Team discovered several problems in the TIFF library. The Common Vulnerabilities and Exposures project identifies the following issues: Several stack-buffer overflows have been discovered. A heap overflow vulnerability in the JPEG decoder may overrun a buffer with more data than expected. A heap overflow vulnerability in the PixarLog decoder may permit an attacker to execute arbitrary code. A heap overflow vulnerability has been discovered in the NeXT RLE decoder. An loop was discovered where a 16bit unsigned short was used to iterate over a 32bit unsigned value so that the loop would never terminate and continue forever. Multiple unchecked arithmetic operations were uncovered, including a number of the range checking operations designed to ensure the offsets specified in TIFF directories are legitimate. A flaw was also uncovered in libtiffs custom tag support which may result in abnormal behaviour, crashes, or potentially arbitrary code execution. For the stable distribution (sarge) these problems have been fixed in version 3.7.2-7. For the unstable distribution (sid) these problems have been fixed in version 3.8.2-6. We recommend that you upgrade your libtiff packages. Solution : http://www.debian.org/security/2006/dsa-1137 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2007 Michel Arboi |
||
|
Cables, Connectors |

Bare S100 CPU Replacement for ALTAIR 8800 IMSAI 8080 JAIR Single Board Computer
$42.00
MITS ALTAIR 8800 Original Vintage Microcomputer
$6000.00
MITS ALTAIR 8800 88-2SIO S-100 Reproduction Board
$35.00
MITS Altair 8800 Computer Bamboo Reproduction Arduino Tested Working Assembled
$649.99
MITS ALTAIR 8800 Original Vintage Microcomputer S-100 Buy It Now $5999
$5999.00
S-100 backplane motherboard bare PCB 9 slot (for Altair/IMSAI)
$30.00
MITS ALTAIR 8800 Original Vintage Microcomputer with 14 boards - Buy It Now
$9500.00
1974 Early Microcomputers by MITS Altair 8800's Ed Roberts HP-9810 Mark-8 Scelbi
$55.00
Vintage Altair 8088 CPU Wire Wrapped S100 Card w Mon EPROM circuit board #T71
$99.00
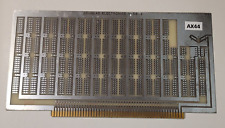
Altair MSAI Douglas Electronics 11 DE Prototype Card S100 circuit board #AX44
$69.00
|
||
|
No Discussions have been posted on this vulnerability. |