|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Debian Local Security Checks >> [DSA1056] DSA-1056-1 webcalendar Vulnerability Assessment Details
|
[DSA1056] DSA-1056-1 webcalendar |
||
|
DSA-1056-1 webcalendar Detailed Explanation for this Vulnerability Assessment David Maciejak noticed that webcalendar, a PHP-based multi-user calendar, returns different error messages on login attempts for an invalid password and a non-existing user, permiting remote attackers to gain information about valid usernames. The old stable distribution (woody) does not contain a webcalendar package. For the stable distribution (sarge) this problem has been fixed in version 0.9.45-4sarge4. For the unstable distribution (sid) this problem will be fixed soon. We recommend that you upgrade your webcalendar package. Solution : http://www.debian.org/security/2006/dsa-1056 Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is (C) 2006 Michel Arboi |
||
|
Cables, Connectors |

Digi View Gold NewTek Color Digitizer 3.0 for Commodore Amiga w/ Software AS IS
$44.99
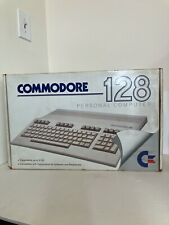
Commodore 128 Personal Computer C128 with Power Supply Fast Load Cartridge
$220.00
MOS 6502 CPU for Commodore VIC 20 Computer & 1541 & 1571 Tested US SELLER
$12.99
UNTESTED Commodore Plus/4 PAL Computer Genuine No Cables Clean
$100.00
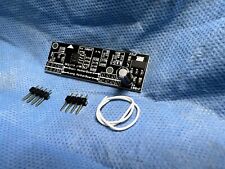
Commodore 64 and 128 (C64 / C128) RF Modulator Replacement
$14.99
Commodore 128 Slim 64k Video Ram Upgrade 41464-10 18Pin w/Sockets and TESTED
$9.95
Commodore SX-64 KEYBOARD ONLY GOOD CONDITION SX64 C-64
$199.00
$200.00
Vintage Commodore 128 Personal Computer w/Box 1987 Untested As Is Rare
$249.99
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
|
||
|
No Discussions have been posted on this vulnerability. |