|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> ColdFusion Double-Encoded Null Byte Information Disclosure Vulnerability Vulnerability Assessment Details
|
ColdFusion Double-Encoded Null Byte Information Disclosure Vulnerability |
||
|
Tries to retrieve script source code using ColdFusion Detailed Explanation for this Vulnerability Assessment Summary : The remote web server is affected by an information disclosure vulnerability. Description : The remote host is running Abobe Macromedia ColdFusion, a product for developing and deploying web applications. The version of ColdFusion installed on the remote host permits an attacker to view the contents of files not interpreted by ColdFusion itself and hosted on the affected system. The problem is due to the fact that with ColdFusion, URL-encoded filenames are decoded first by IIS and then again by ColdFusion. By passing in a filename followed by a double-encoded null byte and an extension handled by ColdFusion, such as '.cfm', a remote attacker can may be able to uncover sensitive information, such as credentials and hostnames contained in scripts, configuration files, etc. See also : http://labs.idefense.com/intelligence/vulnerabilities/display.php?id=466 http://archives.neohapsis.com/archives/fulldisclosure/2007-01/0199.html http://www.adobe.com/support/security/bulletins/apsb07-02.html Solution : Upgrade to ColdFusion MX 7.0.1 if necessary and apply the appropriate patch as described in the vendor advisory referenced above. Network Security Threat Level: Low / CVSS Base Score : 2.3 (AV:R/AC:L/Au:NR/C:P/I:N/A:N/B:N) Networks Security ID: 21978 Vulnerability Assessment Copyright: This script is Copyright (C) 2007 Tenable Network Security |
||
|
Cables, Connectors |

Vintage 5362 IBM System/36 Mini-Computer Mainframe 5291 2, CRT Terminal DM12N501
$249.99
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection - UNTESTED
$65.00
6 Vintage Computer Tape Reels mainframe 3200 5000 data ibm magnetic processor
$99.00
IBM Type 4869 External 5 1/4in Floppy Disk Drive Mainframe Collection
$145.99
Cray Research Supercomputer Cray X-MP ECL Logic Board
$149.99
Digital DEC LK201BA Terminal Keyboard RJ11 Connection Mainframe
$44.95
VINTAGE IBM Type 4869 External 5 1/4" ~ Floppy Disk Drive Mainframe ~
$159.99
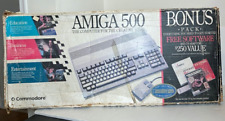
Commodore Amiga 500 Computer w/Mouse and Amiga A520 RF Modulator As Is Untested
$299.99
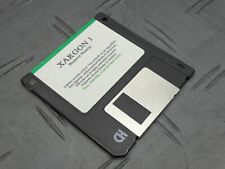
Xargon 1 Beyond Reality RARE Game Floppy 3.5” Floppy Mainframe Collection
$349.99
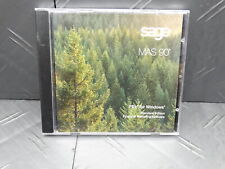
Sage MAS 90 Software for Windows Financial Reporting Mainframe Collection
$339.99
|
||
|
No Discussions have been posted on this vulnerability. |