|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Claroline extAuthSource Parameter Array Remote File Include Vulnerability Vulnerability Assessment Details
|
Claroline extAuthSource Parameter Array Remote File Include Vulnerability |
||
|
Tries to read a local file with Claroline Detailed Explanation for this Vulnerability Assessment Summary : The remote web server contains a PHP script that is affected by a remote file inclusion attack. Description : The remote host is running Claroline, an open-source, web-based, collaborative learning environment written in PHP. The version of Claroline installed on the remote host fails to sanitize input to the 'extAuthSource' parameter array before using it to include PHP code in the 'claroline/inc/claro_init_local.inc.php' script. Provided PHP's 'register_globals' setting is enabled, an unauthenticated attacker may be able to exploit this issue to view arbitrary files on the remote host or to execute arbitrary PHP code, possibly taken from third-party hosts. See also : http://www.gulftech.org/?node=research&article_id=00112-09142006 http://www.claroline.net/wiki/index.php/Changelog_1.7.x Solution : Either apply the security patch to version 1.7.7 or upgrade to Claroline 1.7.8 or later. Network Security Threat Level: Medium / CVSS Base Score : 6 (AV:R/AC:H/Au:NR/C:P/A:P/I:P/B:N) Networks Security ID: 20056 Vulnerability Assessment Copyright: This script is Copyright (C) 2006 Tenable Network Security |
||
|
Cables, Connectors |

Vintage 1991 Hewlett Packard DeskJet 500 Printer Manual Bundle W Floppy Disk
$23.99
Vintage Apple Macintosh Power Supply Part Number 631-5105-A
$39.99
Vintage Sony VAIO C1 MSX PCG-C1MSX computer with rare luggage bag + OG BOXES
$599.99
Computer Lab International 122 Key Vintage Keyboard PS/2 TESTED
$88.88
Vintage Apple Mac Sony MP-F75W-01G 2MB 3.5" Floppy Disk Drive Parts Or Repair
$35.99
Quantum Prodrive 40S For Vintage Macintosh AS IS With Cables
$39.99
VINTAGE DEC DIGITAL DISK FOR RK 05 HARD DRIVE / DECPACK 2200 BPI-16
$95.00
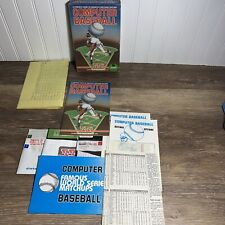
Vintage COMPUTER BASEBALL GAME- SSI- Retro- 48k Atari, Commodore 64 Floppy Disk
$35.00
VINTAGE 1992 NEWPORT SYSTEMS 700-0002-001 REV E GREAT CONDITION
$99.99
Junk Drawer Vintage 1991 Adobe Type Manager Floppy Disk Lot of 3 - For Apple Mac
$40.00
|
||
|
No Discussions have been posted on this vulnerability. |