|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Denial of Service >> Chameleon SMTPd overflow Vulnerability Assessment Details
|
Chameleon SMTPd overflow |
||
|
Acertains if smtpd can be crashed Detailed Explanation for this Vulnerability Assessment It was possible to crash the remote SMTP server by issuing the HELP command followed by a too long argument. This problem may permit a possible hacker to prevent you from sending or receiving e-mails, thus preventing you to work properly. Solution : Update your SMTP server. Network Security Threat Level: High Networks Security ID: 2387 Vulnerability Assessment Copyright: This script is Copyright (C) 1999 Renaud Deraison |
||
|
Cables, Connectors |

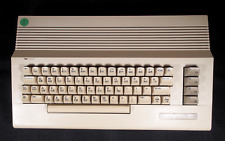
Retro Commodore 64c Computer System Tested 1980s C64c Plus Manuals
$181.75
$240.00
Commodore 128 Personal Computer C128 with Power Supply Fast Load Cartridge
$220.00
Commodore SX-64 Computer & Power Cord Only SX64 C64
$399.00
$87.24
Commodore VIC 20 power cord (NEW REPLACEMENT POWER CORD AND CONNECTORS)
$14.99
$200.00
Commodore 64 2 in 1 Diagnostic & Dead Test Cartridge Fully Assembled USA seller
$19.99
TeensyROM Cartridge for Commodore 64/128: MIDI, Fastload, Emulation, and Network
$65.00
1984 Commodore home Computer Video Color Monitor Model 1702
$252.00
|
||
|
No Discussions have been posted on this vulnerability. |