|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Windows >> CesarFTP stores passwords in cleartext Vulnerability Assessment Details
|
CesarFTP stores passwords in cleartext |
||
|
Acertains the presence of CesarFTP's settings.ini Detailed Explanation for this Vulnerability Assessment The remote host has the program CesarFTP.exe installed. There is a design issue in the program which makes it store the username and password of the FTP server in cleartext in the file 'settings.ini'. Any user with an account on this host may read this file and use the password to connect to this FTP server. Solution : None Risk : Low Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Tenable Network Security |
||
|
Cables, Connectors |

Lot Of Two Vintage Apple Macintosh Computers Models 128k M0001 For Parts
$250.00
Apple Mac Powerbook Duo 230 Vintage Laptop
$60.00
Vintage Apple Macintosh SE Case - Empty Shell - Housing retro project
$60.00
Apple Macintosh ASK M0116 Vintage Keyboard Alps Keycaps (INCOMPLETE)
$14.99
VINTAGE APPLE MACINTOSH POWERBOOK 180 ( M4440) Powers On
$100.00
Apple Studio Display Monitor M2454 15" vintage Mac LCD
$80.00
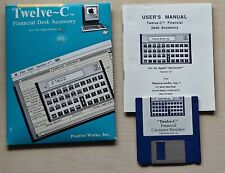
Vintage Apple Macintosh Calculator Twelve-C (HP 12C) Software
$29.00
Vintage Power Mac G4 1843 / 450MHz / 256MB RAM / ZIP / DVD / NO HDD or Bracket
$60.00
Vintage Orange Micro OrangePC 550 Card PCI Power Macintoshes Pentium 233Mhz
$450.00
Apple Macintosh SE/30 M5119 Vintage Mac Computer BAD FLOPPY DRIVE FOR PARTS
$350.00
|
||
|
No Discussions have been posted on this vulnerability. |