|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> Web Servers >> CERN HTTPD access control bypass Vulnerability Assessment Details
|
CERN HTTPD access control bypass |
||
|
Acertains if web access control can be circumvented Detailed Explanation for this Vulnerability Assessment It is possible to access protected web pages by changing / with // or /./ This was a bug in old versions of CERN web server A work around consisted in rejecting patterns like: //* *//* /./* */./* Solution : Upgrade your web server or tighten your filtering rules Network Security Threat Level: High Networks Security ID: Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Michel Arboi |
||
|
Cables, Connectors |

Samsung Galaxy Tab A8 10.5" SM-X200 128GB Wifi Only Tablet Open Box
$149.99
Samsung Galaxy Tab A 8.0" 2019 SM-T290 32GB WiFi Tablet Open Box
$94.99
Samsung S24H851QFN 23.8'' Widescreen QHD PLS LCD LED Monitor With Stand
$49.99
SAMSUNG M393A2G40DB0-CPB 16GB PC4-17000P DDR4-2133 2RX4 ECC
$14.95
Samsung Book Cover Keyboard/Cover Case for Galaxy Tab S9, S9 5g, S9 FE, S9 FE 5g
$120.00
Samsung 860 Evo 250GB MZ7LH250HAHQ SSD
$11.95
Genuine Samsung Book Cover Keyboard for 14.6" Galaxy Tab S8 Ultra | S8 Ultra 5G
$89.99
Samsung Galaxy Tab A9 (X110) 64GB 4GB RAM International Version (New)
$129.99
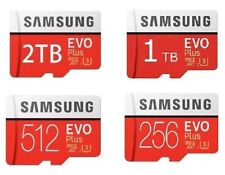
512GB SAMSUNG EVO Plus Micro SD MicroSDXC Flash Memory Card w/ SD Adapter
$21.99
Samsung 16GB 2Rx4 PC3-12800R M393B2G70BH0-CK0 DDR3 RDIMM - SERVER RAM
$8.90
|
||
|
No Discussions have been posted on this vulnerability. |