|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> AtomicBoard file reading Vulnerability Assessment Details
|
AtomicBoard file reading |
||
|
Searches for the existence of remotehtmlview.php Detailed Explanation for this Vulnerability Assessment The remote host is hosting AtomicBoard, a set of PHP scripts. This set of scripts may permit a possible hacker to read arbitrary files on this host by supplying a filename to the 'location' argument of the file index.php. Solution : Upgrade WebCalendar 0.9.42 Network Security Threat Level: High Networks Security ID: 8236 Vulnerability Assessment Copyright: This script is Copyright (C) 2003 Tenable Network Security |
||
|
Cables, Connectors |

For Lenovo IdeaPad 3 15IIL05 15IML05 15ADA05 15ARE05 Palmrest Keyboard Touchpad
$59.25
For Lenovo Yoga 910-13IKB USB C Charging Port Board with Cable NS-A901 US
$138.04
New For Lenovo IdeaPad Flex 5 14ALC05 Palmrest Keyboard Grey Backlit 5CB1C39900
$142.11
Lenovo ThinkPad T480 14" Touchscreen Laptop i5 256GB NVMe 16GB RAM Win 11 Pro
$249.00
Lenovo - LOQ 15.6" Gaming Laptop FHD - Intel Core i5-13420H with 8GB Memory -...
$629.99
Lenovo Ideapad 1i 15.6" FHD Notebook Intel Core i5-1235U 8GB RAM 256GB SSD
$349.99
Lenovo 100e Chromebook Laptop 2nd Gen | 11.6" HD | MTK 1.7GHz | 4GB RAM | 32GB
$32.00
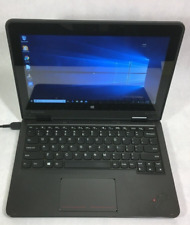
Lenovo ThinkPad Yoga 11e 11.6" 2in1 Touch Intel Core i3 4GB RAM 128GB SSD Win10
$59.00
Notebook Lenovo Slim Pro 9 Laptop, 16" Glass, i9-13905H, GB, 1TB SSD
$1051.99
Lenovo ThinkPad 14" Laptop Computer Core i7 16GB RAM 256GB SSD Windows 10 Pro
$229.99
|
||
|
No Discussions have been posted on this vulnerability. |