|
|
Vulnerability Assessment & Network Security Forums |
|||||||||
|
If through a vulnerability assessment, a network security issue is detected for the vulnerability below, applying the appropriate security patches in a timely matter is very important. If you have detected that your system has already been compromised, following CERT's Network Security recovery document will assist with recommended steps for system recovery. Home >> Browse Vulnerability Assessment Database >> CGI abuses >> Alt-N WebAdmin Multiple Remote Vulnerabilities Vulnerability Assessment Details
|
Alt-N WebAdmin Multiple Remote Vulnerabilities |
||
|
Checks for the version of Alt-N WebAdmin Detailed Explanation for this Vulnerability Assessment The remote host is running Alt-N WebAdmin, a web interface to MDaemon mail server. The remote version of this software is vulnerable to a cross site scripting vulnerability due to a lack of filtering on user-supplied input in the file 'useredit_account.wdm' and the file 'modalframe.wdm'. A possible hacker may exploit this flaw to steal user credentials. This software is also vulnerable to a bypass access vulnerability in the file 'useredit_account.wdm'. A possible hacker may exploit this flaw to modify user account information. A possible hacker need a valid email account on the server to exploit both vulnerabilities. Solution : Upgrade to WebAdmin 3.0.3. Network Security Threat Level: Medium Networks Security ID: 12395 Vulnerability Assessment Copyright: This script is Copyright (C) 2005 Tenable Network Security |
||
|
Cables, Connectors |

2 Vintage Atari 1040STf COMPUTER
$120.00
Vintage Atari 800XL ~ Home Computer in Original Box ~ Tested and Working
$149.90
Atari Power Cube 800XL, 600XL, 65XE, 130XE USB-C Power Supply PSU
$11.25
Atari 400/800/XL/XE Computer SIO2PC - PC/Mac Disk Drive Emulator Adapter/Device
$15.25
Atari 800XL Computer with Chroma Added - Original Box - Tested and Working 100%
$225.00
A8picoCart Atari 130 / 65 XE 800 / 1200 XL XEGS multicart UnoCart clone game
$32.95
Atari 600xl excellent condition - Video and RAM upgrades. 800XL compatible
$255.00
Atari - STEREO TEK Three Dimensional Glasses - with software - complete in box
$2495.00
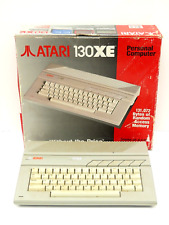
Atari 130XE Personal Retro Gaming Computer PC Complete in Original Box
$299.99
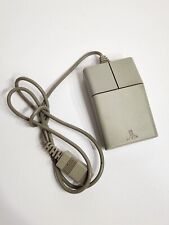
Vintage Atari STM1 Rollerball Two-Button Mouse Serial A2915282515
$69.99
|
||
|
No Discussions have been posted on this vulnerability. |